Security
How is marble non-custodial?
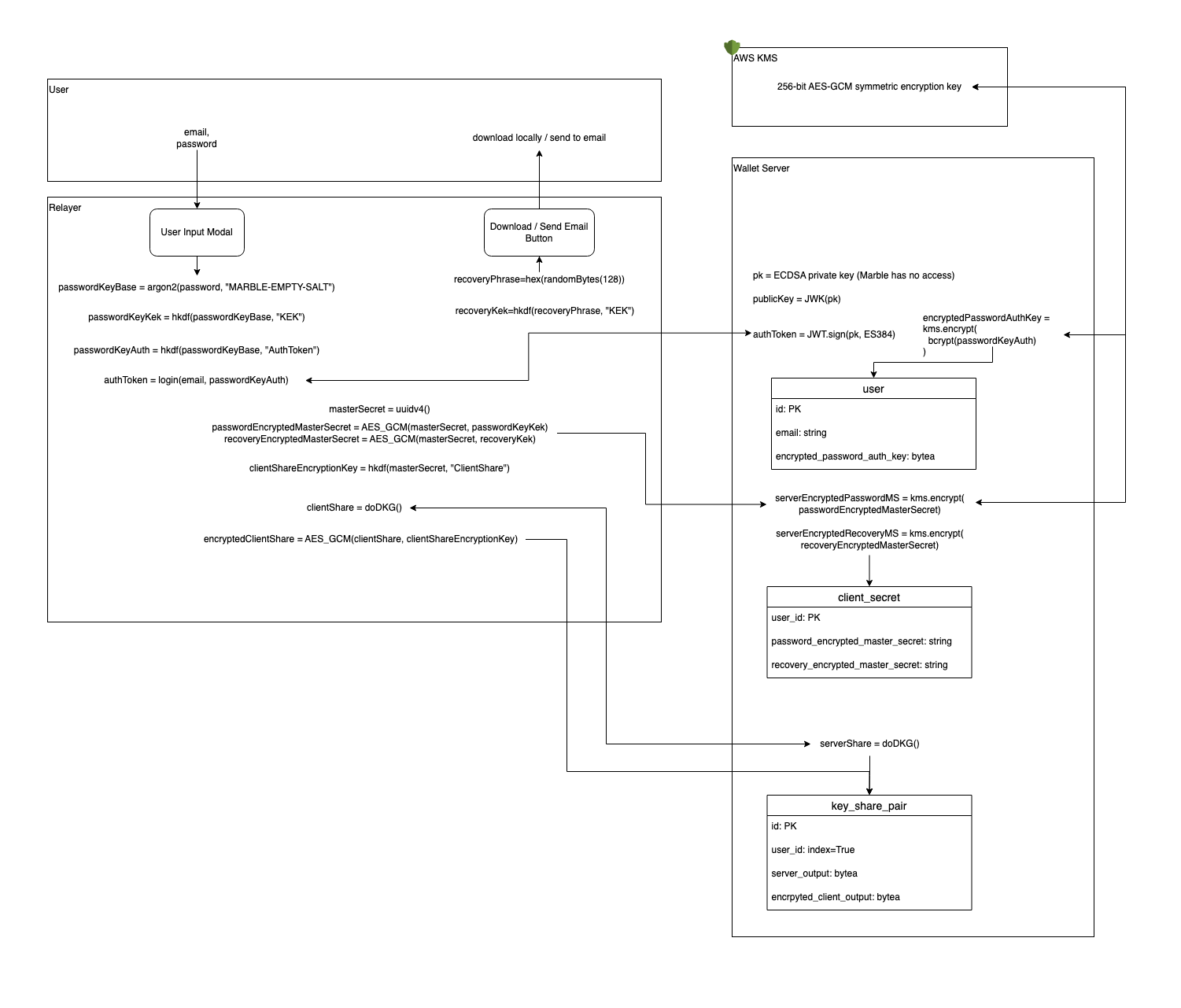
Marble uses a combination of client-side cryptography and threshold signatures to safeguard your wallet. The screenshot shows the cryptographic functions we use and the flow for how it works. The following explains the idea in plain English:
- Client-side cryptography:
- We generate a secret on the client side.
- We use a hash value derived from the user's password to encrypt the secret. This encrypted value gets saved in our database.
- We also generate a separate hash value derived from the user's password. This second hash value of the password gets saved in our database.
- When the user logs in, we check the match of the hash, and return the encrypted value. The user is able to decrypt the encrypted value on the client side.
- Recovery Key is saved in a process similar to the user's password - the server never sees the user's Recovery Key.
- Threshold signatures
- Instead of a regular wallet which uses one private key, we use a new cryptographic technology called Threshold Signatures (which is a form of Multi Party Computation - MPC) that allows us to independently generate multiple private shares. These shares need to work together in order to sign transactions.
- We encrypt the user's share with the secret mentioned in the client-side cryptography above, and store the encrypted value on our server. Since the secret values are only exposed client-side, Marble never has access to the user's wallet.
In order to prevent (or significantly slow) brute force attacks in the event our database is compromised, we encrypt all sensitive information (encrypted secret using the recovery key derived key, encrypted secret using the password derived key, hash of the user's password) that can be brute-forced with an HSM-backed key on the cloud.
Our architecture relies on our server, but it allows the user to access their accounts seamlessly across their devices like they would access their web2 accounts. Adding additional authentication steps like two-factor authentication on high value transactions are on our roadmap.
In the future, we may remove the password requirement completely and instead use a network of nodes or another third party to protect your key. If this is something you care deeply about, please send us a note at team@marblewallet.com